XDR: Beyond the buzzword
What it is, isn't and should be
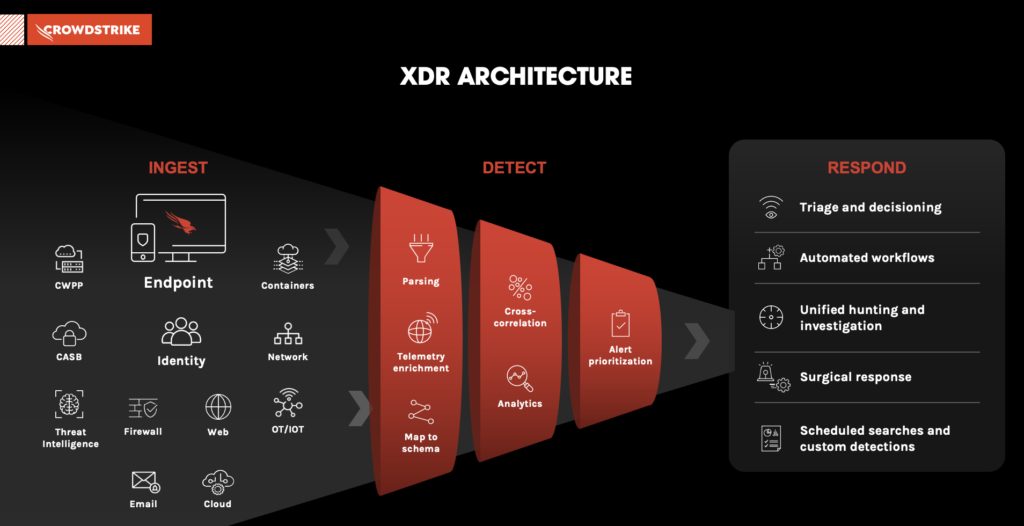
Extended detection and response, or XDR, is more than an industry buzzword. It’s a strategic approach to cyber security. It brings together disjointed products, data and processes to provide holistic visibility and context that helps security teams prioritize the right alerts in order to detect and respond to the most sophisticated threats effectively.
XDR checklist
Recognize what XDR is and arm yourself with 5 questions to avoid fauXDR.
XDR 101
See the top 3 reasons you need XDR and how it differs from EDR and MDR.
What XDR isn’t
Learn what cyber’s new favorite acronym, XDR, is, isn’t and should be.

"… good XDR lives and dies by the foundation of good EDR."
Adapt or Die: XDR Is on a Collision Course with SIEM and SOAR

What’s the difference between endpoint detection and response (EDR) and extended detection and response (XDR)? Does XDR replace EDR? IT and security professionals might be asking themselves these questions. Successful XDR starts with a solid EDR foundation. With the endpoint in its many forms as both an entry point and target for adversaries, having a modern endpoint security solution is critical. XDR builds on that by unifying telemetry from across the security stack into a single console to improve detection and response times.
EDR is the path to XDR
See why successful XDR starts with detecting threats on the endpoint.

Clarity to XDR market confusion
Move from hype to reality and learn why XDR is more than a rebranding effort.

Making the move to XDR
Learn how to connect the dots between siloed security tools to reduce your risk.

Industry analyst views
Delivering innovative, industry-leading solutions is a testament to CrowdStrike's commitment to protecting our customers from today's threats.
See how we stack up in these key analyst reports.
Why CrowdStrike Falcon® XDR
With scalable endpoint and XDR solutions, CrowdStrike can help wherever you need it. CrowdStrike Falcon® XDR, built upon our industry leading Endpoint Protection Platform, enables you to optimize your security stack and stop breaches.